C
Technical overview
The following architecture picture shows the high-level design of the Qt Insight components deployed to customer's AWS environment.
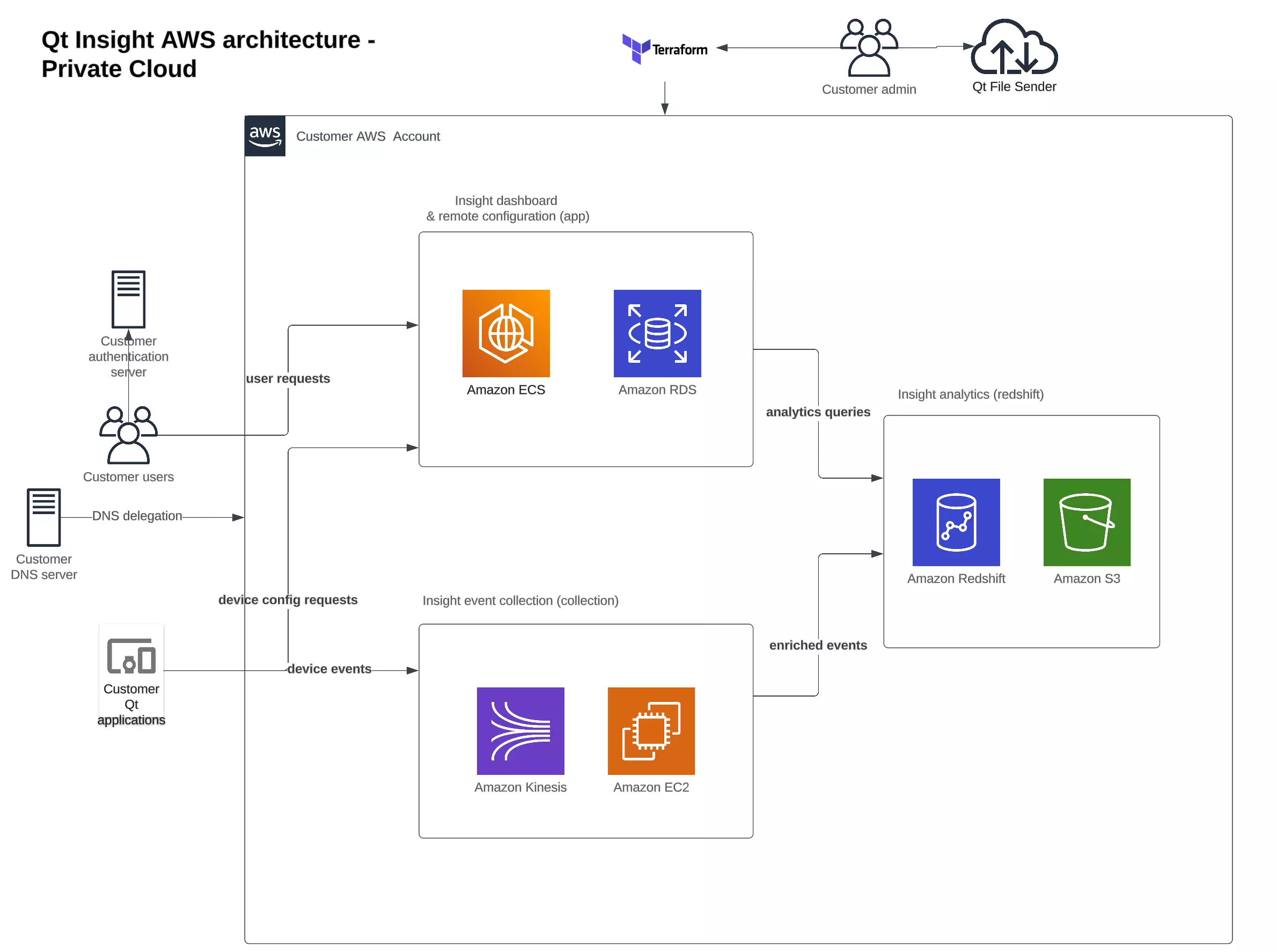
- AWS account. A customer-managed AWS account. You can create multiple environments with different accounts.
- VPC/availability zones. All subnets (public, private, isolated) are configured to two availability zones (a, b) within a region.
- User requests. An Elastic Load Balancer (ELB) routes the user requests from the Insight Console to the corresponding Elastic Container Service (ECS) task. Transport layer security (TLS) connection is terminated at the ELB. An AWS Certificate Manager (ACM) is used to store the SSL certificates.
- Elastic Container Service (ECS). Qt Insight dashboard components are hosted using AWS ECS. This consists of frontend (graphical user interface), backend (dashboard API) and remote-config (handles device remote configuration endpoint and token verification)
- Device events. An ELB routes the device events sent by the Tracker Library to the data pipeline hosted on Amazon Elastic Compute Cloud (EC2) instance.
- Device config requests Qt Insight Tracker can fetch configuration updates from Insight. The requests are routed to Insight remote-config ECS task. remote configuration can be set up by Insight organization admin.
- Data pipeline. After event processing, the enriched events are loaded into the S3 Data Lake and Insight Analytics Database (AWS Redshift).
- Databases. Qt Insight backend uses the App Database (PostgreSQL on AWS RDS) and Analytics Database (Redshift).
- Database network configuration. Databases are deployed to an isolated subnet (without an Internet Gateway).
- Modules and images. Application images and Terraform modules are fetched from Qt File Sender. These are distributed as a single TAR archive. For more information on how to upload application images to an AWS Elastic Container Registry (ECR), see pushing private images.
Available under certain Qt licenses.
Find out more.